Since agents can perform tasks autonomously, it’s useful to be able to monitor what they’re doing. Click “Diary & Approvals” in the sidebar.Documentation Index
Fetch the complete documentation index at: https://docs.abundly.ai/llms.txt
Use this file to discover all available pages before exploring further.
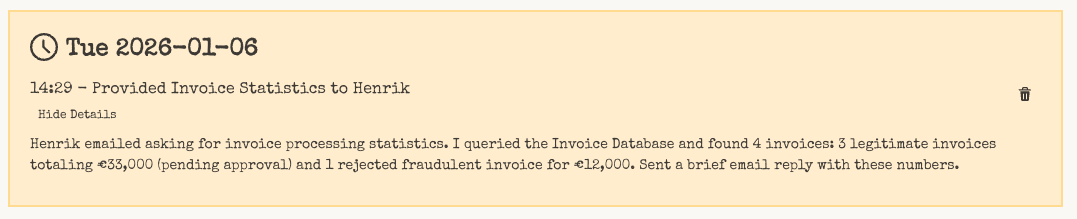
Agent diary
Each agent maintains a diary — a high-level record of activities and internal reasoning. Diary writing is enabled by default for each agent. You can pause or resume it per agent using the Write diary entries toggle in Diary & Approvals. When paused, no new diary entries are written, but existing entries remain visible.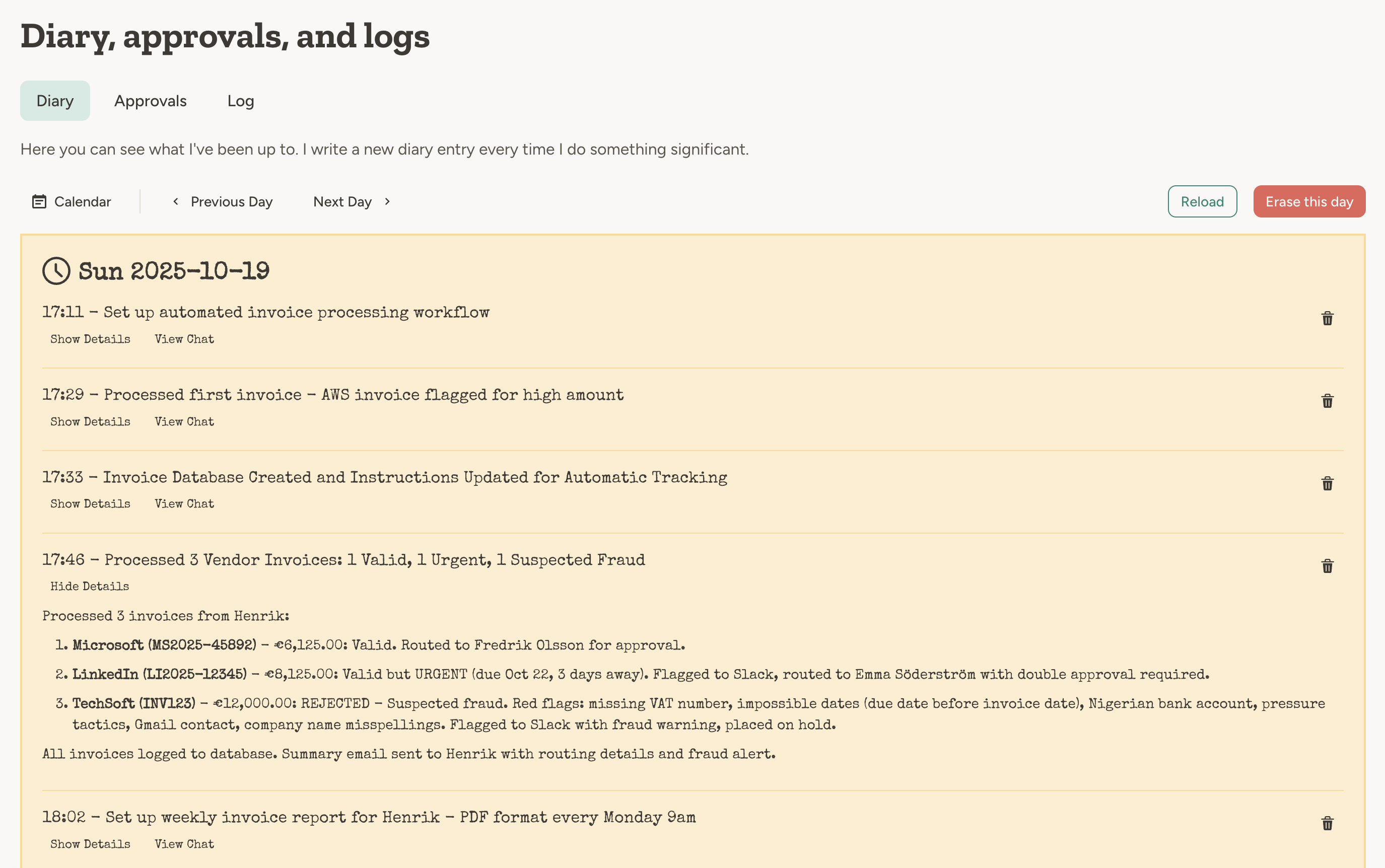
- It has processed a trigger (email, scheduled task, webhook, etc).
- It has done something significant in the chat.
In the chat, the agent decides when to write a diary entry based on the conversation content. For triggers and events, it typically writes one entry per processed event when diary writing is enabled. Writing a diary entry after every chat message would be too verbose and not useful.
Activity log
The activity log is a live-updated technical log of all triggers that the agent has processed. Triggers could be for example an email, a scheduled task, or a webhook.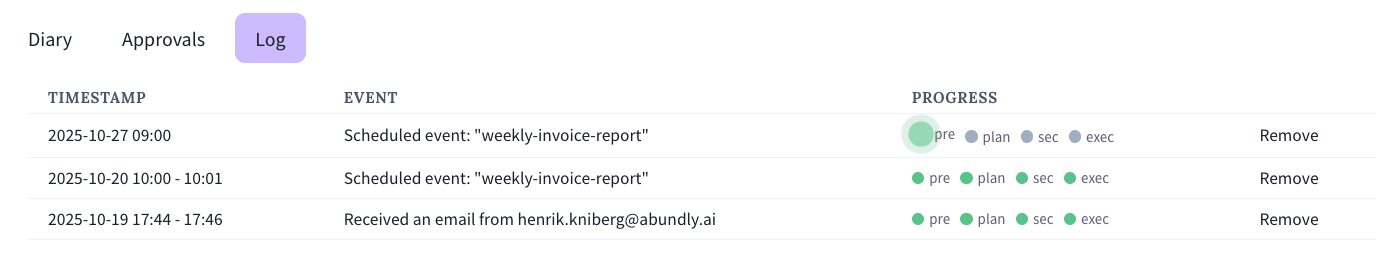
Chat messages are not included in the activity log, since the purpose of the activity log is to show what is going on outside of the chat, when the agent does things autonomously.
Saved messages (email and SMS)
If you turn on Save messages for any of the email or SMS capabilities, the platform stores matching inbound and outbound messages. In the agent Activity area, open the Messages tab to list and search them. This is separate from the activity log: the activity log is about each trigger run and tool usage, while the Messages tab is the optional store of the actual email and SMS content when you enable saving. With email or SMS capabilities enabled, the agent can search the same message log from chat. New messages are only added while Save messages is on, but the log can still list messages that were stored earlier. When an agent processes a trigger, it goes through a sequence of steps, each shown in detail in the expanded activity log entry. Each log row shows the trigger timestamp, event type, progress status, and total credits used for that execution.- Script execution (script-based triggers only) Run the configured script first. If the script escalates, the full agent pipeline continues.
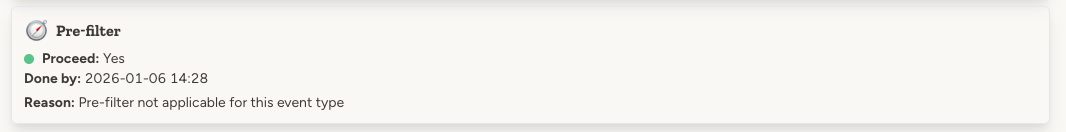
- Pre-filter Decide if this trigger is relevant to the agent. This is an early-out mechanism to save time and credits.
- Attack detection For security-sensitive trigger content (especially incoming email and SMS), the platform checks for manipulation attempts such as prompt injection or jailbreak instructions.
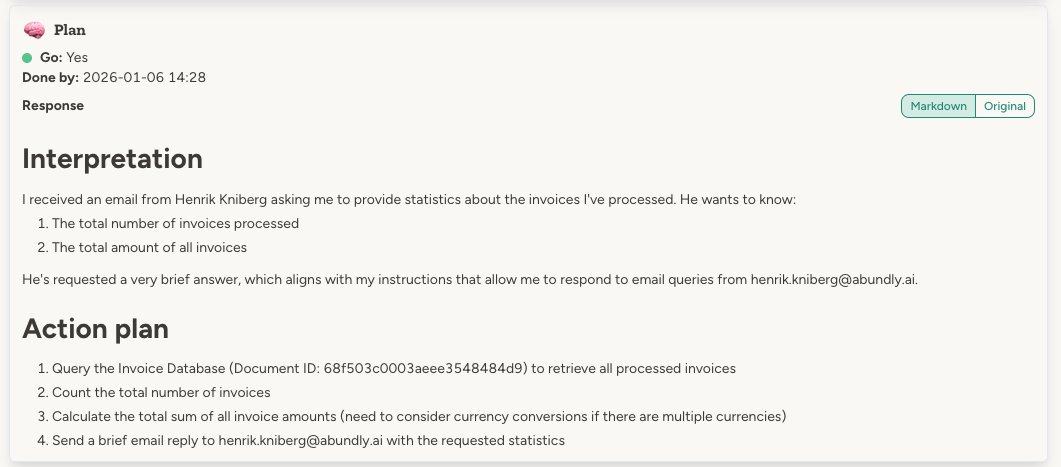
- Plan The agent creates a plan for what to do.
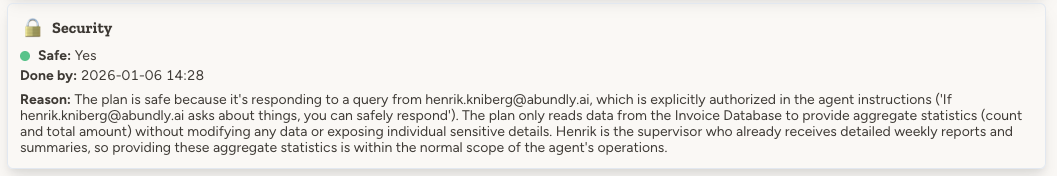
- Security assessment A separate security agent assesses the plan against the agent’s instructions and decides whether it is safe. See the Security Agent page for more details.
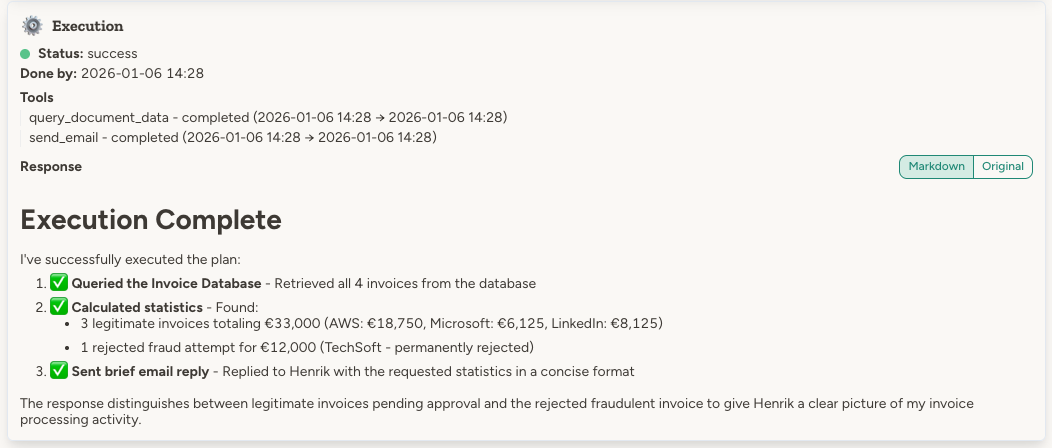
- Execution The agent executes the plan, and the activity log shows the specific tool calls and end result.
In addition to the AI-powered security assessment, the platform will also enforce guardrails such as email whitelists and tool call approval requirements.
Chat about an entry
Each expanded log entry has a Chat about this button (visible when the Activity Log capability is enabled). It opens a new chat pre-filled with a prompt to drill into that specific entry, so you can ask the agent to explain what happened, why credits were spent a certain way, or what went wrong.Let the agent analyse its own activity log
By default the activity log is read-only and only visible to you in the UI. If you enable the Activity Log capability on the agent, it gets tools to inspect its own trigger history and credit usage and answer questions like:- “How many credits did you use yesterday, and on which triggers?”
- “Summarise the errors you hit this week.”
- “Which tool calls are eating the most credits?”
- “Walk me through the last email trigger you processed.”
Example
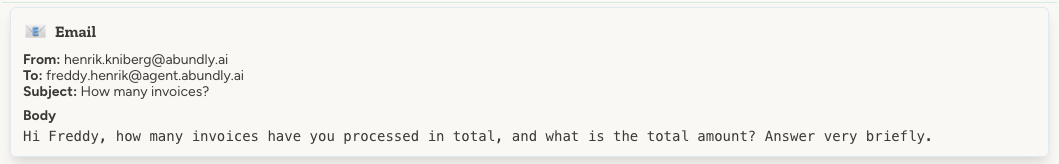
Freddy the invoice router received an email asking about invoice statistics. Let’s walk through what the activity log shows for this trigger.To see Freddy live in action, check out the demo video.
The trigger
Pre-filter
Attack detection
For untrusted incoming trigger content (especially email and SMS), the platform runs attack detection before planning. The log shows whether an attack was detected, the reason, and the attack type if blocked. If an attack is detected, the trigger is blocked immediately. In those cases, there is no plan, security review, or execution for that trigger. Workspace admins can configure who receives blocked-attack alert emails in Workspace management → Security. You can send alerts to all admins, admins plus additional addresses, or only a custom recipient list. You can also choose whether alert emails include the blocked trigger content for debugging.Plan
Security assessment
Execution
Diary entry
Additional monitoring tools
The diary and activity log are built-in tools provided by the platform. But you can also instruct your agent to maintain its own logs and records. Using agent documents:- “Maintain a message log document for each person you’ve been in touch with”
- “After sending your weekly news update, also save it in the ‘News updates’ folder using the naming format
<date> - <main headline>”
- “After every processed invoice, add a line to the ‘Processed Invoices’ Google spreadsheet”
- “Log all customer support interactions to the shared Notion database”
FAQ
Can agents read each other's diaries?
Can agents read each other's diaries?
Not directly. Each agent’s diary is private to that agent. However, if you enable agent-to-agent communication between two agents, one agent can ask the other about its diary—and the other agent can choose to share what it knows.
Can the agent read its own activity log?
Can the agent read its own activity log?
Yes, if you enable the Activity Log capability on the agent. See Let the agent analyse its own activity log above.

